In years past, a person’s voice was a singularly distinguishing feature. Your voice was the culmination of a lifetime of experience, with different twinges of local accent and types of articulation based on the regions you had lived in and the dialect of the people around you.
Today, however, a person’s voice is not nearly as definitive an original asset as it once was. Whereas voice used to be one of the most trusted forms of identity, that assumption is now collapsing as AI-generated voices become nearly indistinguishable from real ones.
The Collapse of Voice as Proof of Identity
Recent advancements in voice cloning mean that even a few seconds of audio can be enough to convincingly replicate a person’s voice. This has made traditional authentication methods obsolete, as a person’s once distinguishing vocal qualities can now be emulated by AI-powered tools.
As a result of these shifts, organizations are being forced to rethink identity entirely. Many have begun moving toward systems in which verification occurs before trust is ever granted, and where voice is no longer a credible credential in its own right. What was once a “trust but verify” model has now become a flat-out “zero trust” model.
Ankur Malik, Director of Engineering at Hudson Data, reports, “What’s going to happen now is… zero trust. First, verify and then give minimum access.”
This marks a reversal in how trust has historically functioned. Voice used to act as a shortcut. It collapsed uncertainty into recognition. If it sounded right, it was treated as right. Malik explains how quickly that assumption breaks down: “If your boss is calling you and you recognize his or her voice, you say, ‘OK, boss.’ There’s trust there. But once that trust starts shaking, you start thinking, hey, is this person really that person who is saying he is just because the voice signature matches?”
The moment of hesitation is new. It signals a transition from instinctive trust to analytical verification. What replaces it is not a better single signal, but a system of signals. Malik says, “Voice is one signal. Overlay it with dozens of more signals, with thousands of more properties, and then assign a composite score.”
This transforms identity into a data problem. Trust is no longer inferred, but calculated. The issue is that many organizations are still treating voice fraud as a marginal concern rather than a systemic one. Malik points out that the problem is often hidden in plain sight. “We currently are underacting on this topic. Companies label it as a risk. A lot of times they write it off and say it’s a loss, so the real numbers are still not in the open.”
When fraud is absorbed instead of analyzed, it fails to trigger meaningful change. It becomes a cost of doing business rather than a signal of structural vulnerability. And yet, the underlying capability has already proven itself. Malik illustrates, “In 2019, the famous UK case where a fraudster cloned the CEO’s voice and called up, ‘hey, I need 250k right now,’ and the exec said, ‘okay boss, I’m transferring…’ Just think of what we can do today.”
The implication is direct. Voice has become a liability when treated as proof.
Why Humans Are Still Essential
The capabilities of these AI vocal features have generated considerable suspicion and paranoia on all sides.
Andrew Melnychuk-Oseen, founder of Saga Corp, surmises of modern vocal interactions, “We’re going into a world where we’re not going to know if either of us is real.” This uncertainty, in his view, is the natural consequence of technological convergence. “Our communication channels are soon to be flooded with completely AI-generated communications… our old governance systems cannot police this.”
Melnychuk-Oseen connects voice cloning to a broader breakdown in institutional control. He illustrates, “When somebody can download a voice cloning tool and run an agent that you can’t shut down… how do you police it?”
Even benign use cases carry disproportionate risk. And historically, societies have consistently mishandled these transitions. Melnychuk-Oseen contends, “People usually do not exercise restraint with new technology. It often takes generations to adapt and use it responsibly.”
Despite the sophisticated and highly technological nature of more recent fraudulent attacks, the most effective defenses remain human-driven: awareness, skepticism, and verification protocols. However, as technology continues to evolve, some viable AI-based defense systems have become quite viable as well.
For example, Saga Corp is building a decentralized “Proof of Human” system using Bitcoin signatures to authenticate users. This creates a trusted layer for human-to-human interaction, enabling users to filter out bot activity. This transition mirrors past record-keeping revolutions that caused institutional chaos and required generations to adapt. Saga aims to accelerate this adaptation to avoid a similar period of conflict.
Decentralized Identity and “Proof of Human”
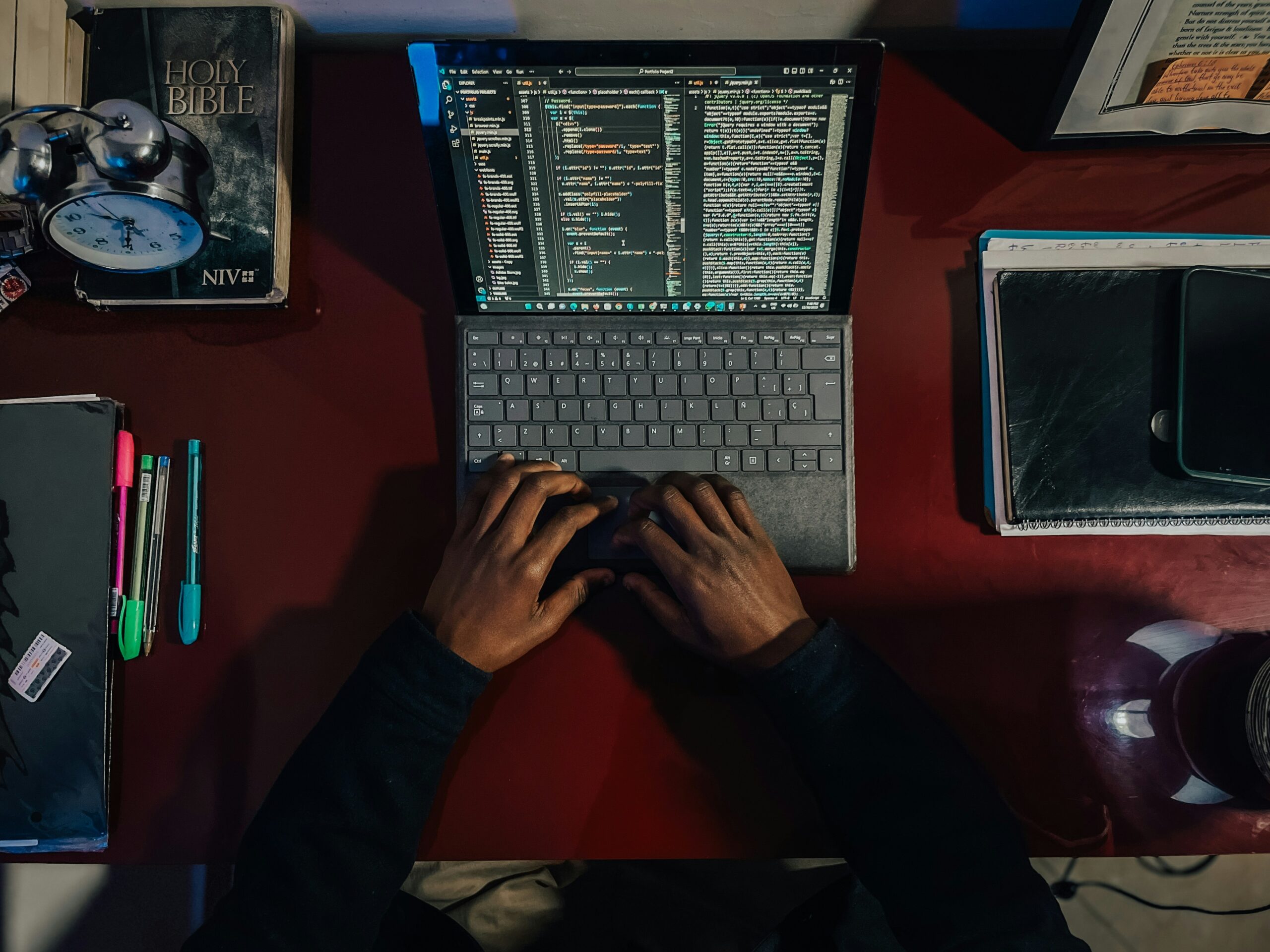
Elsewhere, new approaches aim to verify humanity itself by creating decentralized systems that distinguish real users from AI agents. While attackers have historically utilized AI much more effectively than defenders, for example, enabling “script kiddies” to execute sophisticated social engineering campaigns for wire fraud, this doesn’t mean there is no recourse.
John Coursen, the leader of Fortify Cyber, says, “The primary defense is back to basics human training on out-of-band verification.” This approaches the issue from a more immediate, tactical perspective. In his view, the imbalance between attackers and defenders is already clear.
This gap is not just about access to tools, but about intent. Attackers adapt quickly because the payoff is direct and measurable. Coursen ties this to a long-standing reality in cybersecurity. He illustrates, “You can spend a billion dollars on security… and all it takes is somebody to open an attachment in an email that they shouldn’t have opened.”
Voice cloning sharpens an existing weakness. It gives attackers a more convincing way to trigger the same behavioral responses. “Voice used to be a major unit of trust. It is being used for multi-factor authentication, wire approvals, major account changes… and now that’s being replicated,” Coursen says.
The mechanics of these attacks are often straightforward, which is part of what makes them effective. “They will port your number, call a family member, and say, ‘I’m traveling, and I need you to wire me money…’ and we’ve gotten a lot of calls like that.”
Coursen describes how the barrier to entry is significantly lowered. “All I need is an 11-second clip to get an 80% accurate clone of your voice and use it.” Public content becomes a liability. Any recorded voice can be repurposed. Meanwhile, the actors behind these attacks are becoming more organized and more efficient.
Despite the rampant misuse of voice cloning, Coursen’s recommendations are grounded in behavioral discipline rather than technical escalation. That includes simple but effective practices. He says, “If you get a phone call, hang up, call them back on a different platform, or use out-of-band communication.”
And even low-tech safeguards work. “We talk about safe words now… like a phrase that only you and your family would know.”
The threat is technologically advanced, but the most reliable defenses remain behavioral. The challenge is not just building better systems, but making sure that people consistently apply them in moments where trust feels natural, and verification feels unnecessary.
Final Thoughts
Voice alone is no longer enough. Organizations are moving toward multi-signal identity systems that analyze behavior, data patterns, and context. Companies must adopt layered verification, train employees on emerging threats, and rethink identity as a dynamic, multi-dimensional problem.
The age of trusting what we hear is over. In a world where voices can be cloned and identities fabricated, the future of security depends on redefining trust itself, before it’s too late.